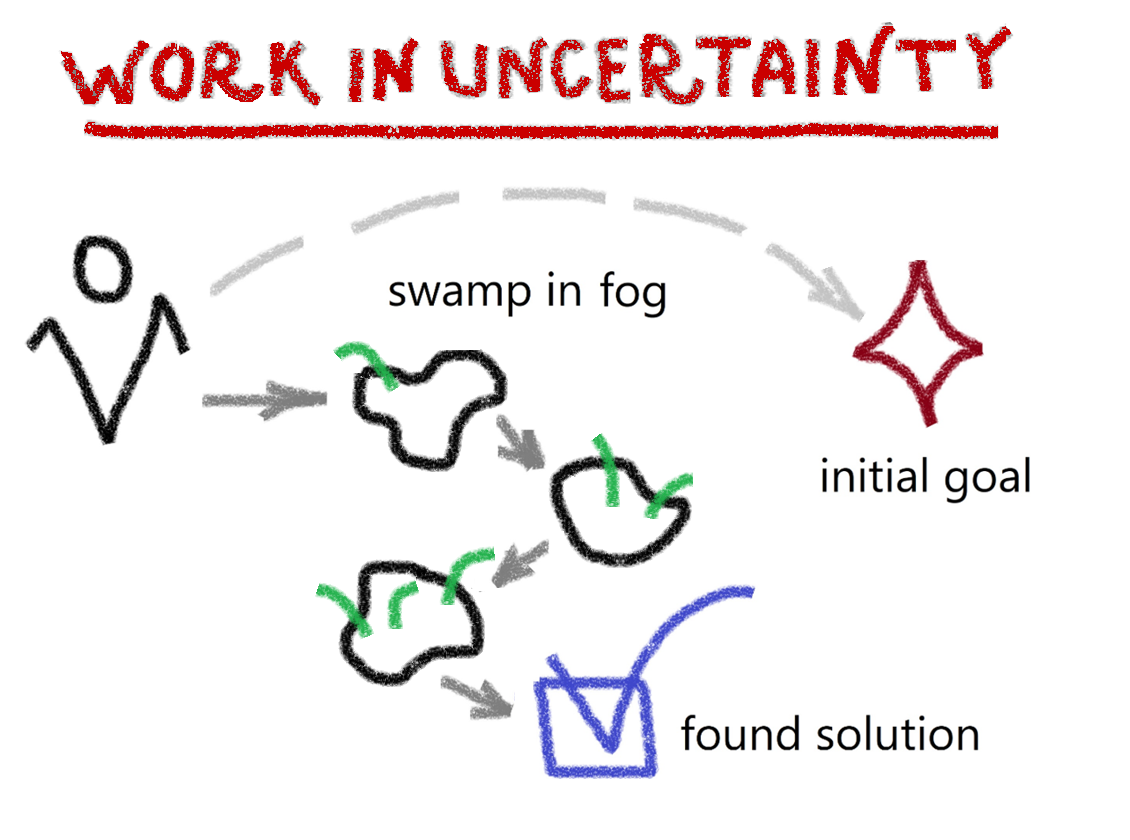
It’s a harsh reality that any investment or security that you have is subject to systematic risk, that’s just the nature of the financial world, with mispricing — causing a divergence between the market price of a security and the fundamental value of that security — a guilty party quite often. This is brought about by the world we now live in, information-heavy, with masses of unstructured data sets and with an infinite number of possible outcomes.
Luckily, there are now methods in place that can combat some of these difficulties and, with any luck, bring the investor a healthy return on their investment.
And it comes in the form of Al-driven, quantum-inspired solutions fuelled by state-of-the-art processors that are able to leverage the unique attributes of quantum physics to solve some of the most, up to now, unsolvable problems, with a handful of startups at the forefront of it.
These include Adaptive Finance Technologies, QuantFi and Zapata Computing which, to a greater or lesser degree, have their own unique approach to investment strategies in the global markets in securities pricing, portfolio optimization, equities, derivatives and the like.
We’ll look now, just at a handful of these whose data readers will be able to find on TQD’s very own data platform, The Quantum Insider (TQI), starting off with the three already mentioned before moving on: